Cybersecurity in the Sea
Introduction
We have been asked to design an innovative product or service with respect to the state of the art.
Starting from the PERSPECTIVES ON CYBER OPERATIONS and CYBER ANAGEMENT PERSPECTIVES seminars, in which it was explained how the national defense created a structure to manage marine security, we asked ourselves: why not create a similar structure for all civil and state societies? And so our idea was born.
Customer Segments
Since the dawn of civilization, the sea has been a medium for the exchange of goods, cultures, ideas and innovations: this is precisely the idea behind our solution.
In fact, as a fundamental requirement, we look for entities which like us believe that the problem of IT security is not only a matter of the individual but concerns everyone.
Specifically, our infrastructure is open to all entities, both public and private, which manage all or part of their activities at sea, such as: cargo and tourist ship companies, oil and gas extraction stations and infrastructures that manage the positioning and the
Obviously, we focus a lot on joining ports, which we believe to be the central fulcrum of maritime trade, as billions of goods and information pass through them every day, making them, unfortunately, one of the main targets of cyber attacks.
We initially want to open the membership to the private bodies mentioned above and then integrate public and state companies, in order to create a heterogeneous and international structure that allows all those who carry out activities at sea to navigate safely.
Problem Statement
In 2010, an oil-drilling platform en route from its construction site in South Korea to Brazil was attacked by a computer virus: the identification of the problem and its solution took 19 days.
In August 2011, as a result of a series of cyber-attacks against the Iranian maritime line server, a quantity of valuable information was lost, such as accounting documents, cargo and handling data, shipping addresses, causing confusion, to the point that some loads were lost or redirected to the wrong ones.
In July 2014, the University of Texas demonstrated that it was possible to hijack a ship by falsifying a GPS signal, so as to deceive the onboard navigation system.
Not only ships, but also port infrastructures are not secure. At the end of 2013, it turned out that, in the Belgian port of Anversa, a criminal organization dedicated to drug trafficking had managed to interfere with port operations for about two years. After violating the port’s computer systems, the criminals were able to ship containers of drugs, weapons and money wherever desirable, all of this without arousing any suspicion in the competent authorities.
Those listed above are only a tiny part of the possible examples of cyber attacks that affect the maritime reality.
In addition to threats to the transportation or the oil system, the marine environment can be the scene of other criminal activities or cyber warfare aimed at the network of about 380 submarine fiber optic cables. The cabling guarantees approximately 97% of the international data traffic and voice communication, as well as daily financial payments for a total of 10,000 billion dollars.
For this reason, a protection system for all marine structures is not only convenient but also necessary.
Our infrastructure will be able to provide the necessary support and security to each registered entity; in particular, we will follow two tracks: prevention and action.
As for prevention, we provide safe, cutting-edge and always up-to-date tools to prevent cyber-attacks such as malware infection and attacks capable of sabotaging the on-board instrumentation or information gathering attacks.
On the other side, in order to provide active security we have a SOC that is always active and ready to receive alerts from the equipment provided to any registered body (or directly by the body itself). This will allow us to respond promptly and in a very short time to the attack and to warn the competent authorities in order to secure the vehicle.
To conclude, using the classification of Maslow we will describe what are the needs to be met for our customers:
- Safety:
- Health and safety of people: in the first place, we can only put the safety and health of people who, due to the consequences of yber-attacks, can be endangered, especially at sea.
- Protection of information and data: in our opinion, the information and data of our customers re a factor of vital importance, for this reason we will protect and make them secure.
- Resources: cyber-attacks, especially for ports and erchant ntities, can make you lose a lot of money or resources.
- Law: we want to avoid our customers from incurring penalties for not having had an dequate level of security.
- Esteem:
- Status, Responsibility and Reputation: one of the main consequences of being a victim of a yber-attack is the loss of reputation and responsibility in the eyes of its customers, with the consequent loss of money and income.
Existing Alternatives
At the moment there are various organizations and companies that have tried to find a solution to this problem and each of them works on its own.
Currently, the most used solution is to apply policies and procedures, standards, guidelines and training of the personnel.
Some of them also do Risk Assessment and apply the only certifiable standard available at the moment, Wärtsilä, which is a network for collecting data from various companies for protection against cyber attacks.
There are companies that do not care about cyber attacks or do not protect their assets for some reason.
There are various organizations that could potentially be our competitors such as IMO (International Maritime Organization), OCIMF (Oil Companies International Marine Forum) and IMCA (International Maritime Contractors Association) but they do not have a unified system to protect themselves from cyber attacks. Actually they have absolutely no system but apply procedures and standards to protect themselves and rely more on staff training to prepare them to use the on-board equipment appropriately.
Competitors:
- Oil Companies International Marine Forum:
- Procedures for the management of patches and software.
- Processes and guidelines for identifying and mitigating cyber threats.
- Procedures for managing passwords.
- Development of a cybersecurity awareness-raising and training plan for all staff involved.
- International Maritime Organization
- Risk assessment of all IT and OT devices, both on board and on land.
- Security policies related to the use of external storage devices.
- Policies and procedures on the use of networks and communications by the crew.
- Policies and procedures on the monitoring and updating of navigation and communication systems.
- Policies on the authorization criteria for the use of remote connections.
- Inventory of all OT systems.
- Internet access policies, setting out restrictions when operations are being carried out on board.
- Preparation of contingency plans for emergency responses.
- International Maritime Contractors Association
- Active management of the inventory of devices and authorized and unauthorized software.
- Bastioning of final and network devices.
- Evaluation and continuous solution of vulnerabilities.
- Defence against malware.
- Wireless network access control.
- Data recovery capacity.
- Evaluation of team’s cybersecurity skills and training program.
- Control of access to network ports.
- Control of the use of administrative privileges.
- Perimeter defence.
- Maintenance, monitoring and analysis of logs.
- Access control based on the principle of Need to know, where the user only gets access to the resources that are strictly necessary for their work.
- Monitoring and control of user accounts.
- Information protection.
- Response and management of cybersecurity incidents.
- Secure network engineering.
- Conducting penetration tests to assess the strength of an organization’s defences.
In the absence of a real system and even more of a system that unifies several companies in a single protection network, our system certainly has a great advantage.
The only system that is currently our competitor is the Wärtsilä network which
Compared to the Wärtsilä network, our network with the blockchain is certainly more secure and efficient in sharing information of compromises of maritime systems, a timeliness that can save not only material damage but also human lives thanks also to our active safety by the SOC. Moreover, it notifies the other nodes of the network of the attack so that they can prepare in time.
Timeliness in repairing damage caused by the attack becomes crucial especially when navigating or trading in the seas of the European Union and the world.
To sum up, compared to the competition we offer a global infrastructure that provides many services and benefits.
First of all, its global being favors the communication of information, in our opinion the most effective weapon to fight and prevent cyber attacks. We also provide an active protection system, which guarantees immediate support to all victims of cyber attacks at sea. Finally, thanks to our blockchain network, we focus on the confidentiality of our customers making every type of communication secure.
In conclusion, our great innovation is that we look not only at the protection of an individual, but at a larger project where everyone is a node of a large network that collaborates and benefits from others making the whole system safer.
Solutions
The solution to the previous problems is the creation of a heterogeneous network of entities where every activity, be it large or small, public or private, can freely register to take advantage of our services.
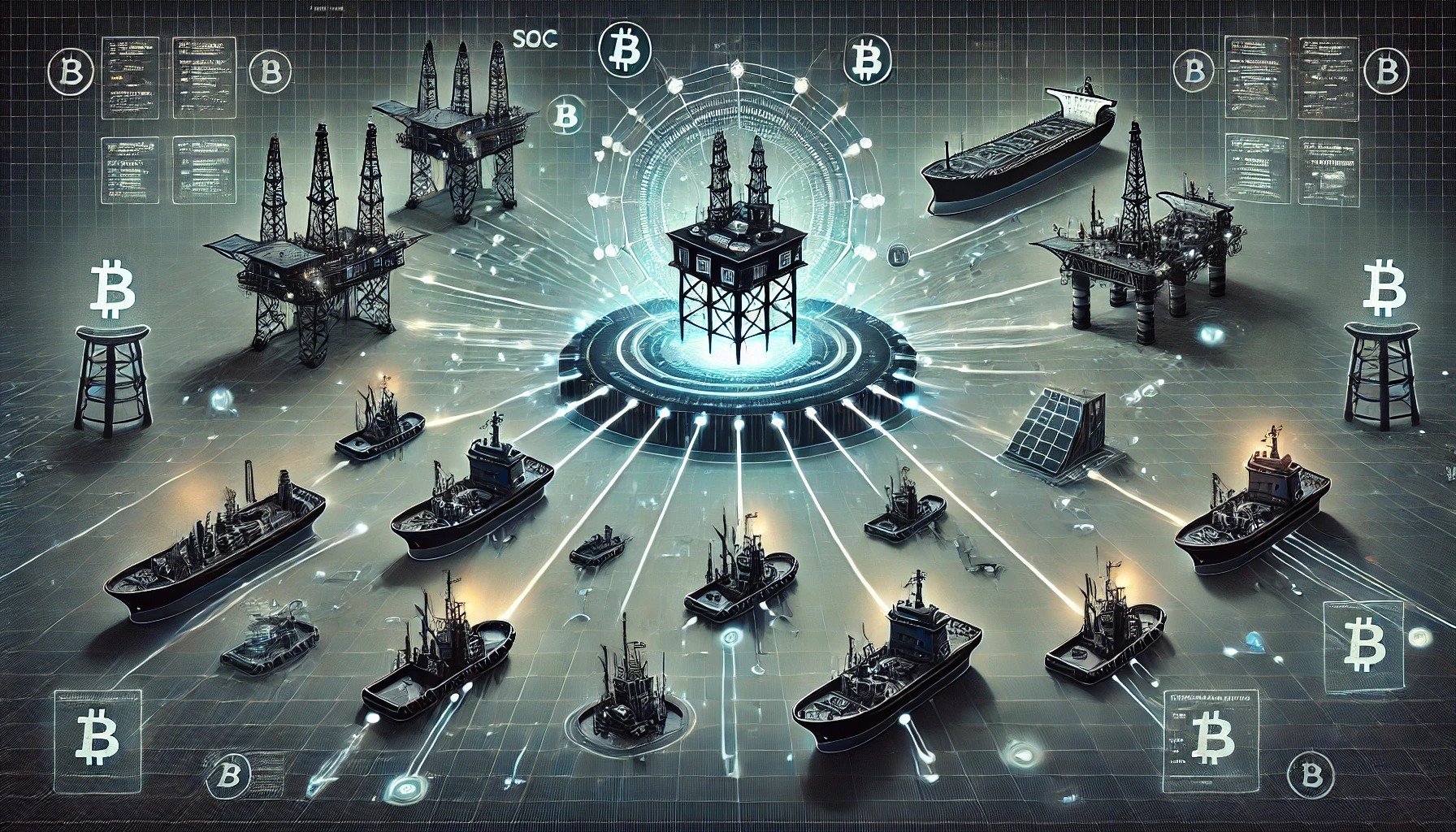
- Network Architecture: We want to emphasise that the innovation part of our solution is in using a blockchain Network. This technology will help us build a “Trusted Network” in which information about the ongoing and previous attacks will be stored securely in a type of data structure (Distributed Ledger) and shared between multiple nodes belonging to the same network. This will allow nodes to have a track on the status of the attacks in real time.A general concept of the Blockchain Network is shown in the picture:
- Network Representation: Let’s have a look at what can be the network architecture in order to have a better understanding of it.
The first aspect to take in account is that the registration to the Network takes place through an annual subscription service, in which the cost is established based on the number of resources to be protected, the number of proprietary equipment to be provided and the size of the perimeter to be protected.As represented in the picture, the network itself consists of the following actors:
- Organization (ORG.): Which is a set of nodes appertaining to the same organization (The org. can consist of a single node).
- Node: Naval platforms (ships, oil platform etc…) / Nodes are connected to the BlockChain Back end as a service via an Application ‘Front end’.
- S.O.C.: The node in charge of the analysis of the attacks. (core system providing the forensic analysis), note that it is possible for an organization to be part of the network without using the S.O.C services (private, ORG. 4) or having just a few nodes use the S.O.C (ORG.3).
- Channels: Channels are a logical structure formed by a collection of nodes. This feature allows a group of nodes to create a separate Ledger, in fact the Ledger on channel ORG_SOC (basically Node_SOC) is different from the one in ORG_ORG as the Ledger on the channel ORG_SOC contains more detailed information about the attack (logs, system report, etc…), information used by the S.O.C to perform analysis (in fact the only nodes capable of receiving detailed reports on the analysis are the one undergoing the attack). on the other hand the ledger on channel ORG_ORG contains only the status of the ongoing attack. To make it short, informations will be sent to the S.O.c in form of a log file (only to the S.O.C) and the result of the diagnosis will be sent only to the attacked node, others nodes will only receive a status message on the ongoing attack (handled/false positive/ongoing).
- Attack Handling: As mentioned above, our solution services follow two tracks: prevention and action.
Action
As a first step, once registered, we will provide our proprietary equipment to each ship, structure or resource established by the contract with the entity. The instrumentation consists of antivirus and IDS always connected to our network and all the necessary devices, such as antennas or parables, to connect to the network. Obviously, in addition to the instrumentation itself, we offer support for correct installation and use.
These tools around the clock will monitor the situation of the resource concerned and will protect it from cyber attacks. In the event that the IDS should detect abnormal behavior in the on-board instrumentation or in the network, it will send an alert directly to our SOC.
Even the same crew or people working on a given resource can contact our SOC as soon as they notice a malfunction or incorrect behavior of on-board instruments.
When the alert is sent, the resource will put itself in a state of danger and communicate it to all other resources on the network (2), so that they can modify their routes in order to not to run into dangers.
As soon as the alert reaches SOC (1), as a first move it will warn the authorities of the state closest to the resource, in order to avoid physical damage in case of sabotage of the on-board instrumentation. In the meantime, it will immediately begin to analyze the malware, determining the type of problem (defining if it is an attack of cyber terrorism, cyber war or other, determining the origin, the consequences and the level of complexity) and, above all, acting promptly remotely on the instrumentation on the resource and providing detailed and precise instructions to the staff in order to stem the problem.
Prevention
Once the SOC post mortem analysis phase is finished, all the information obtained such as signature, hashes, peculiar behaviors, created artifacts and evidence will be sent to the instruments present on all the registered resources (3) via the blockchain.
In this way, the attack will be ineffective on all the other resources registered in our network, as it will be easily detected by our equipment.
Unfair Advantage
What sets us apart from our competitors, is the dedication in protecting navigation tools from cyber attacks , hence to make navigation safe, by ensuring that our product offers advanced, complete and innovative cybersecurity measures.
Our product is unique: it takes advantage of the Blockchain security features to ensure a secure network of ships (and not only) connected together which continuously shares information about the eventual ongoing attacks, in order to keep the entire network constantly alerted in real time.
Using our product, our customers will never be surprised by cyber attacks in the seas and left to handle those attacks on their own, thanks to our secure network of trusted nodes (ships, SOC, etc.) where each node has other nodes back, notifying the network of any ongoing attacks. Because unity is strength and sharing is caring.
And because we care about our customers' financial resources too, we offer to our Customers a friendly approach applying flat prices and customized settings, seeking to make decisions from the customer perspective.
In a massively digitized world, where information is constantly being shared, in various ways and for diverse reasons (fun, education, work), we have chosen to use information sharing in order to create a more alerted and secure working environment for all the sea workers.
Key Metrics
Financial Metrics:
- Profit: this is an obvious metric to tell if we have succeeded and it is one of the most important performance indicators. To better understand how successful our organization is at generating a high return, we still have to analyze both gross and net profit margin.
- Gross Margin: the higher our Gross Margin is the more our company earns by each sales euro. This can help us to invest in other operations.
- Net Profit Margin: the Net Profit Margin will help us to understand how efficient our company is at generating profit compared to its revenue, basically how much of each euro earned translates into profits.
Customer Metrics:
- The number of customers: this is a fairly straightforward indicator. We can understand whether or not we are meeting our customers’ needs by determining the number of customers we have gained and lost, in other words, this metric helps us to understand if we are succeeding or not.
- Customer Satisfaction: making the customer happy is an important metric in order to evaluate our success. If we make the customer happy, they will continue to be our customers. This metric can be measured by including the customer satisfaction scores and percentage of customers repeating a purchase.
- Customer loyalty and retention: having loyal customers is beneficial in many ways. It creates an emotional connection between the parties, and it helps to grow our sales and spread the word about our product. The Retention Rate shows the number of clients who keep using our product over an extended time period and make repeat purchases.
Process Metrics:
- Customer Support Tickets: in order to create the best customer service department in our industry, it is necessary to have a high number of resolved tickets (alert, attack handled) and to have a lower resolution time for those tickets, because it is mandatory for us to be fast in responding to alerts and to give a precise and complete diagnosis of the situation to our client.
References
- https://www.incibe-cert.es/en/blog/cybersecurity-standards-sea
- https://www.maritime-executive.com/blog/yber-security-at-sea-the-real-threats
- https://www.wartsila.com/twentyfour7/innovation/cybersecurity-looks-to-the-cloud-to-protect-data-at-sea
- https://www.gov.uk/government/publications/future-of-the-sea-cybersecurity
- http://www.marina.difesa.it/
- https://cybersecurity.uniroma1.it/node/154
- https://cybersecurity.uniroma1.it/node/96
- https://issuu.com/rivistamarittima/docs/novembre_2019